- Category: August 2013 - Data Protection & Security
 As Glenn Greenwald, journalist at The Guardian, correctly predicted, further NSA unveilings now by far surpass the previous news to the topic. Greenwald published further documents of NSA whistle blower Edward Snowden, which demonstrates the extent of NSA internet surveillance which makes Tempora and Prism look like child‘s play.
As Glenn Greenwald, journalist at The Guardian, correctly predicted, further NSA unveilings now by far surpass the previous news to the topic. Greenwald published further documents of NSA whistle blower Edward Snowden, which demonstrates the extent of NSA internet surveillance which makes Tempora and Prism look like child‘s play.
The Guardian published a presentation last Wednesday, which gives details on the surveillance infrastructure - how it worked as far back as 2008. The documents show that XKeyscore allows analysts to search through vast databases of emails, online chats and the browsing histories of millions of individuals, and is supposed to be the "widest-reaching" internet surveillance system.

Greenwald reports about the latest revelations, which shed light on Snowden's highly controversial statement in his first video interview published by the Guardian: "I, sitting at my desk," said Snowden, could "wiretap anyone, from you or your accountant, to a federal judge or even the president, if I had a personal email", which was denied vehemently by US officials.
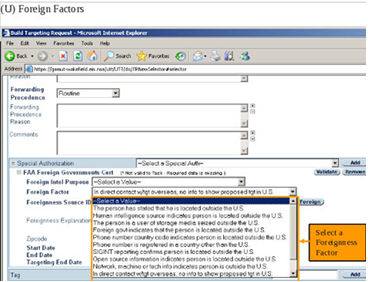
Training materials from the Snowden documents show how it can be used to mine enormous agency databases by filling in a simple on-screen form giving only a broad justification for the search, which is not reviewed again before it is processed.
One of the documents claims that XKeyscore covers "nearly everything a typical user does on the internet", including the content of emails, websites visited, searches and metadata. According to Greenwald, NSA analysts can obtain ongoing "real-time" interception of an individual's internet activity.
XKeyscore provides the technological capability, if not the legal authority, to target even US persons for extensive electronic surveillance without a warrant provided that some identifying information, such as their email or IP address, is known to the analyst.
Another slide called "plug-ins" from a 2012 document describes the various fields of information that can be searched, e.g. "every email address seen in a session by both username and domain", "every phone number seen in a session (e.g. address book entries or signature block)" and user activity – "the webmail and chat activity to include username, buddylist, machine specific cookies etc".
In a second Guardian interview in June, Snowden elaborated on his statement about being able to read any individual's email if he had their email address. He said the claim was based in part on the email search capabilities of XKeyscore, which Snowden says he was authorized to use while working as a Booz Allen contractor for the NSA.
One top-secret document describes how the program "searches within bodies of emails, webpages and documents", including the "To, From, CC, BCC lines" and the 'Contact Us' pages on websites".
To search for emails, an analyst using XKS enters the individual's email address into a simple online search form, along with the "justification" for the search and the time period for which the emails are sought. Another document, a guide from 2010, describes the training NSA analysts received and shows that analysts can begin surveillance on anyone by selecting legal and targeting justifications from a simple pull-down menu.
XKeyscore also allows analysts to monitor a virtually unlimited array of other internet activities, including social media, such as Facebook chats and private messages. Searching HTTP activity by keyword permits the analyst access to what the NSA calls "nearly everything a typical user does on the internet”, enabling them to find out the IP address of anyone visiting a website the analyst specifies.
The quantity of data collected by the NSA is immense. It is yet not completely clear if the extent of data collected differs for different countries around the globe, maybe the recordings are more extensive for countries of special interest?
In 2012, there were at least 41 billion total records collected and stored in XKeyscore for a single 30-day period.
The documents also indicate that US secret services are planning to attack foreign computer systems. XKeyscore enables analysts to access a list of all computers which can be attacked in one country.
What are the surveillance methods of other governments? Are there any restrictions? We probably all need to get used to the idea that there is no privacy, and probably never has been, on the World Wide Web. (Source: http://www.theguardian.com/world/2013/jul/31/nsa-top-secret-program-online-data)
By Anjum Siddiqi


